Demo Mode — curated FINDIT2 test samples
Hidden by default · activate with Shift+D or?demo=1
Likely forged
Multiple regions show strong evidence of editing.
Saudi VAT QR check ✓ verified
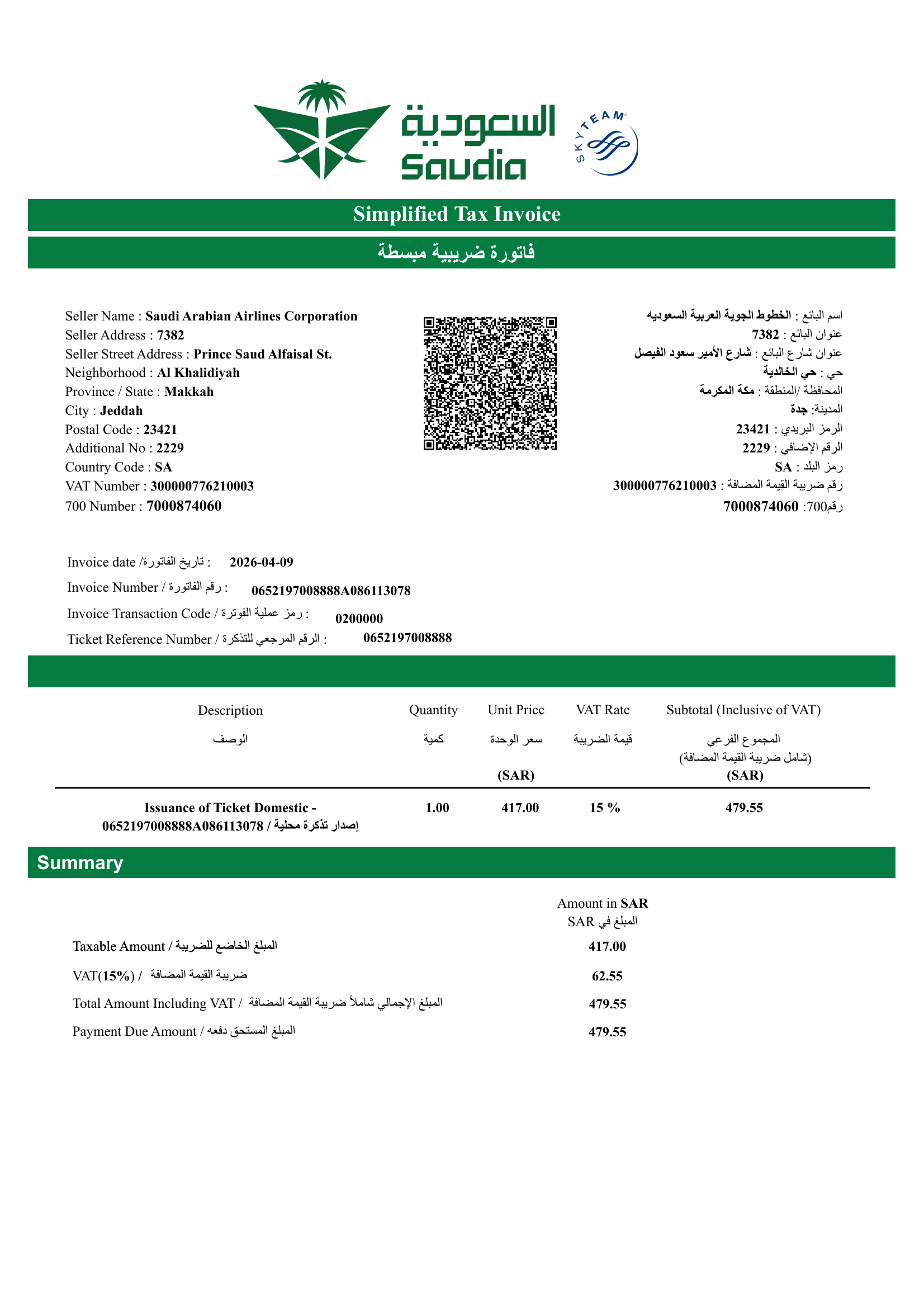
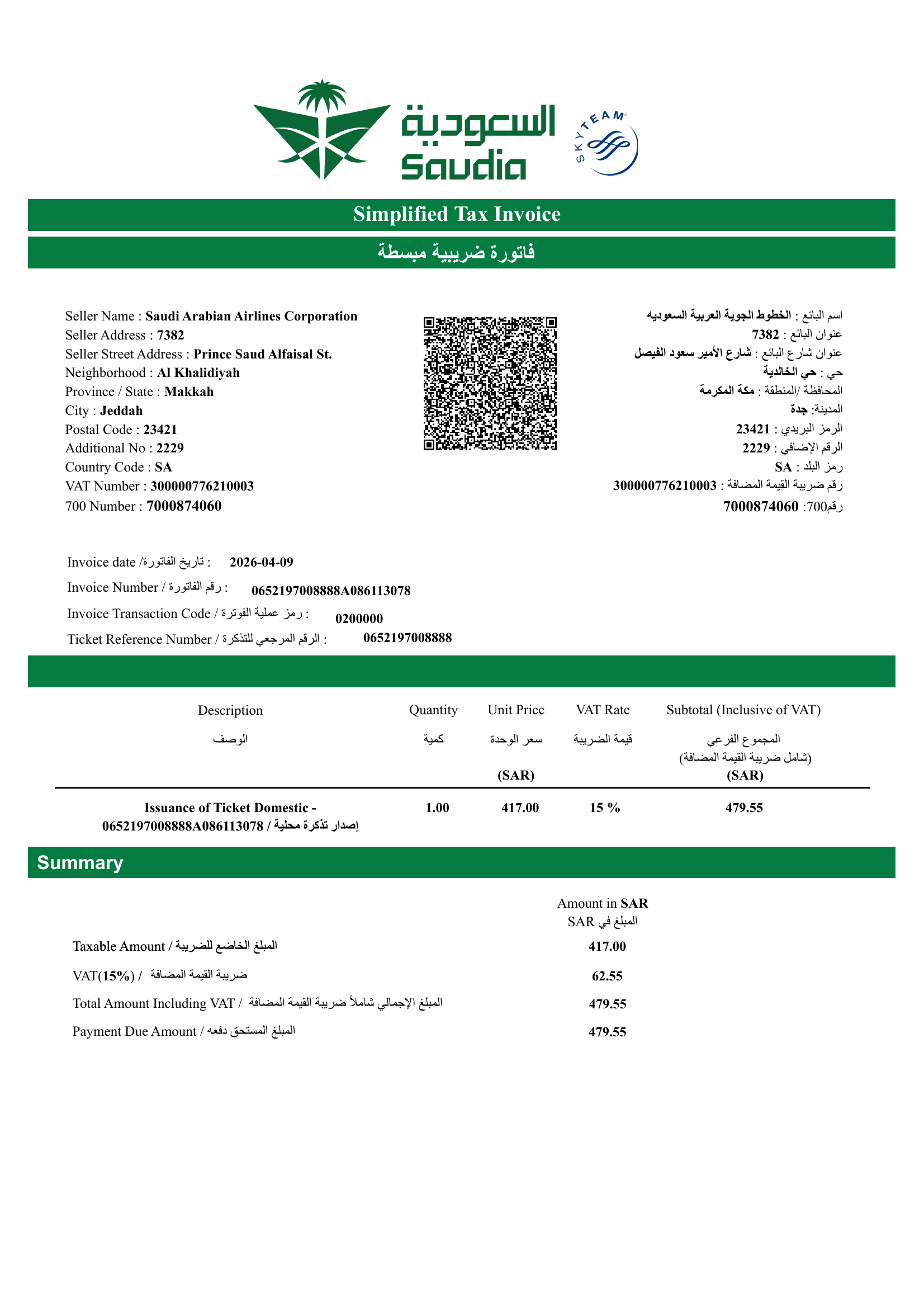
الخطوط الجوية العربية السعوديه|Saudi Arabian Airlines Corporation
· VAT# 300000776210003
· 479.55 SAR (VAT 62.55)
Show all 10 checks & full decoded fields
- payload decodes — Base64 + TLV well-formed; 9 tag(s) found.
- all mandatory tags present — Tags 1 (seller), 2 (VAT#), 3 (timestamp), 4 (total), 5 (VAT) all present.
- VAT number format — 300000776210003 — 15 digits, starts and ends with 3.
- timestamp valid — 2026-04-09T21:17:16Z (parses as ISO 8601).
- amounts numeric — Total 479.55 SAR · VAT 62.55 SAR.
- VAT ≤ total — VAT amount does not exceed invoice total.
- VAT rate ≈ 15% — Implied rate 15.00% (±2pp tolerance from 15%).
- seller name on receipt — 'الخطوط الجوية العربية السعوديه|Saudi Arabian Airlines Corporation' identifying tokens found in OCR'd receipt text (token overlap 100%).
- invoice total matches receipt — QR total 479.55 SAR appears in the receipt (closest OCR value 479.55).
- VAT amount matches receipt — QR VAT 62.55 SAR appears in the receipt OCR.
Key findings
- Multiple regions show strong evidence of editing.
- Showing the top 5 highest-confidence regions (highest score 100%). 403 of 388 text-bearing regions exceeded the model's threshold overall.
- Edit type predicted across the top 5 regions: 3 × copy-paste edits and 2 × deletions / erasures.
- Targeted fields: 4 × Date / store metadata and 1 × Total / payment lines.
- This file is an exact duplicate of one already analysed in this session.
 🔍 Click to zoom
🔍 Click to zoom
 🔍 Click to zoom
🔍 Click to zoom
Suspicious regions
The top 5 highest-confidence regions out of all 403 that exceeded the model's threshold. Hover or click any thumbnail to highlight that 128 × 128 region on the document on the left.
Region breakdown table (5 rows)
| # | Coords | Score | Edit type | Field affected |
|---|---|---|---|---|
| 1 | (1344, 768) |
100% | CPI 55% | Metadata 38% (low conf) |
| 2 | (192, 704) |
100% | CUT 70% | Metadata 50% |
| 3 | (1280, 704) |
100% | CPI 31% (low conf) | Metadata 80% |
| 4 | (1408, 768) |
100% | CUT 49% (low conf) | Total/payment 44% (low conf) |
| 5 | (192, 768) |
100% | CPI 67% | Metadata 45% (low conf) |
Methodology, audit metadata & technical details
saudia__clean.png
SHA-256: 8b710ed87c26…
Size: 1653 × 2337 px
Analysed: 2026-05-11 23:29:59
Model: FraudX v2-multi · ResNet-18 · ep13 · thr=0.08
Approach. ResNet-18 patch classifier (128×128, stride 64) trained on FINDIT2 (Tornes et al., ICDAR 2023). Two auxiliary heads classify the modification technique and the document field; the binary backbone is frozen so the headline patch precision (92.25%) is preserved bit-for-bit while adding explainability. Image-level fraud score is the top-k mean of patch probabilities over text-bearing regions only (edge density ≥ 0.02) — keeps blank regions from poisoning the score.
Class accuracies on the FINDIT2 test set.
- Edit type: CPI 73% · CUT 100% · IMI 38% · PIX 55% · Other 14%
- Field: Total/payment 67% · Metadata 47% · Product 27% · Company 24%
Original technical findings (raw).
- Patch CNN flagged 403 of 388 text-rich patches (top score 1.00).
- Top 5 suspicious regions clustered around image coordinates (1344,768), (192,704), (1280,704), (1408,768), (192,768).
- Predicted modification mix across top regions: 3× CPI, 2× CUT.
- Predicted entity types: 4× Metadata, 1× Total/payment.
- Document is an EXACT duplicate of a file already analysed in this session (resubmission).
